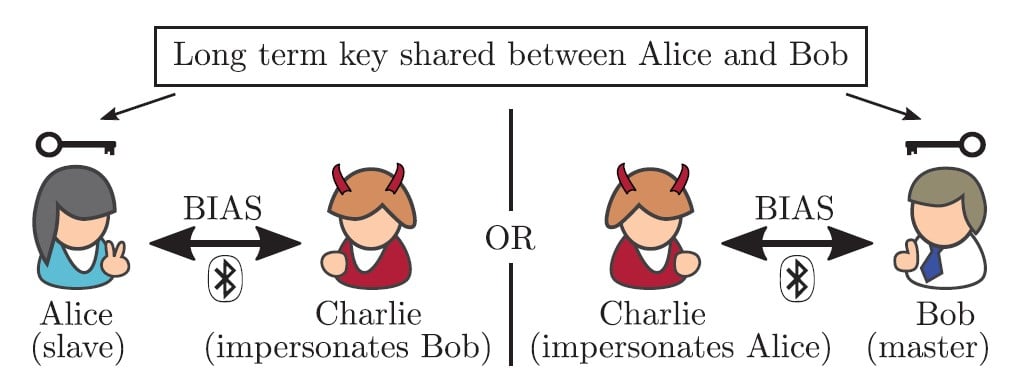
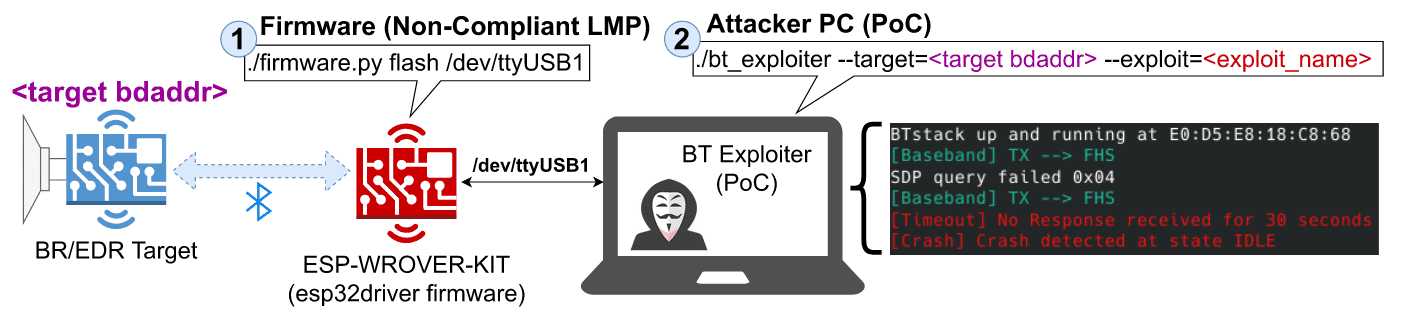
7 New Bugs in Bluetooth Let Hackers Impersonate As Legitimate Device & Launch DDoS Attacks - GBHackers On Security
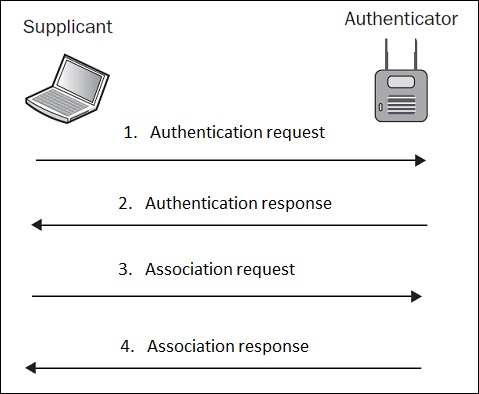
How to hack into mobile phones via bluetooth & How to Hack Wireless Internet Connections in 3 Easy Steps PresentedBy Pradosh H.S. - ppt download
GitHub - crypt0b0y/BLUETOOTH-DOS-ATTACK-SCRIPT: Script for quick and easy DOS-attacks on bluetooth devices for pentest purposes

Kali Linux Advanced Wireless Penetration Testing: Bluesmack – Bluetooth DoS Script|packtpub.com - YouTube





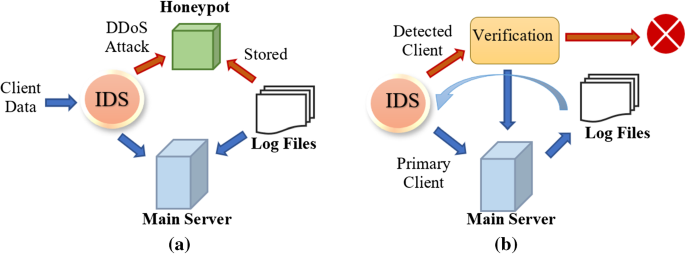
![What is a DoS Attack and How to DoS Someone [Ping of Death] What is a DoS Attack and How to DoS Someone [Ping of Death]](https://www.guru99.com/images/EthicalHacking/DOS_Attacks3.png)