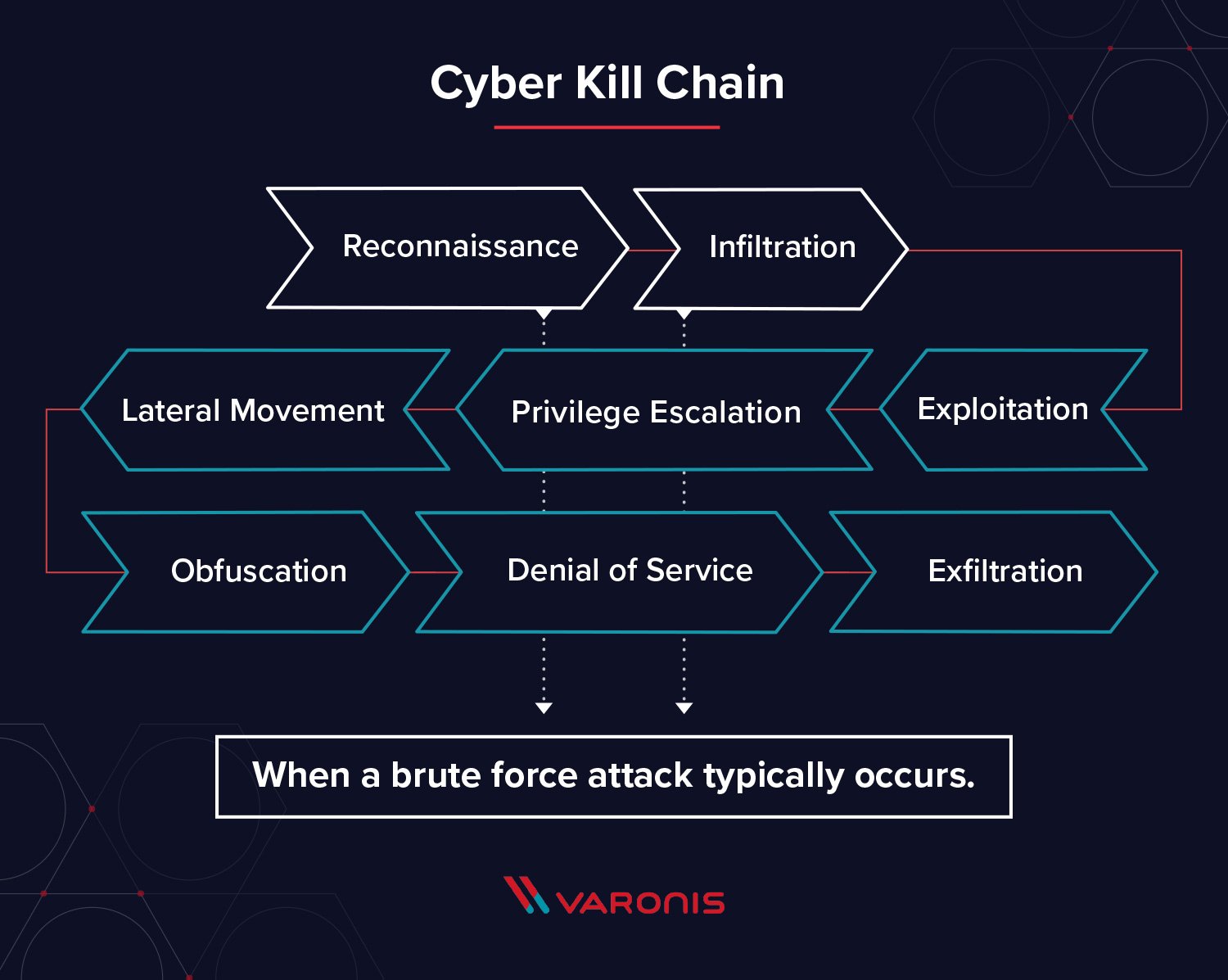
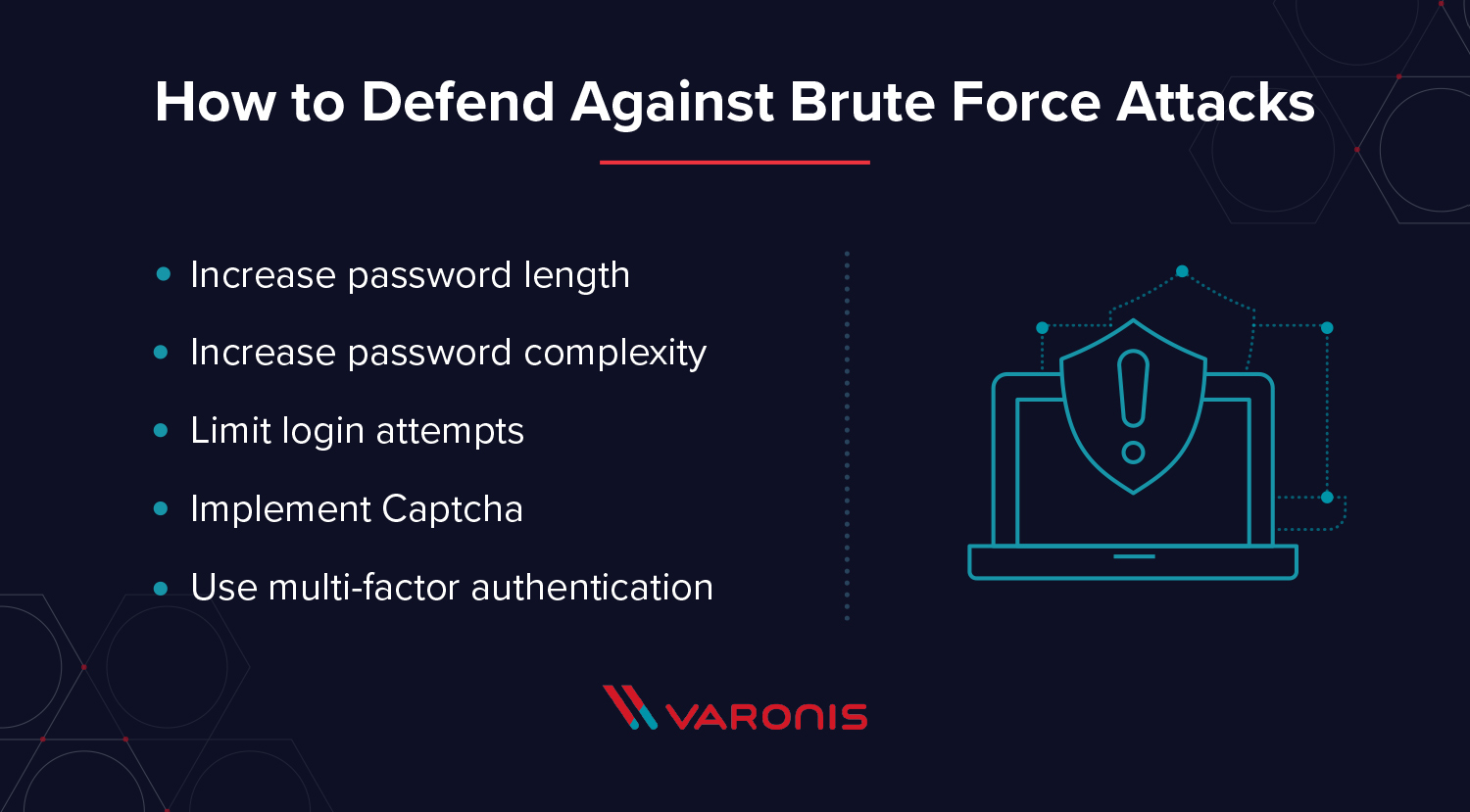
Security hacker Password Brute-force attack, thief, computer Network, people, computer Program png | PNGWing
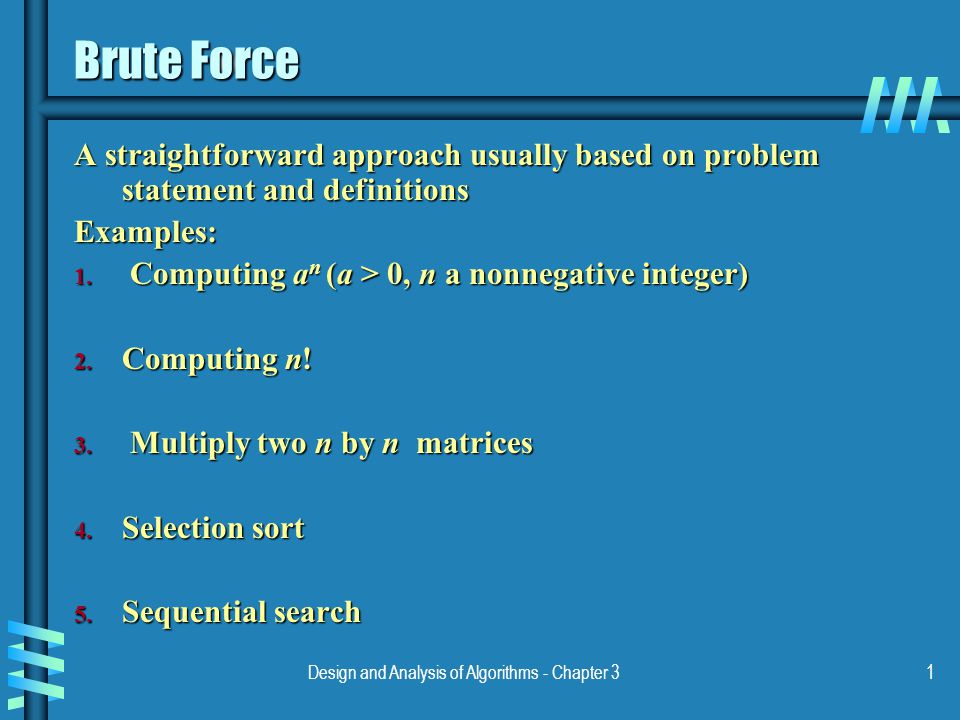
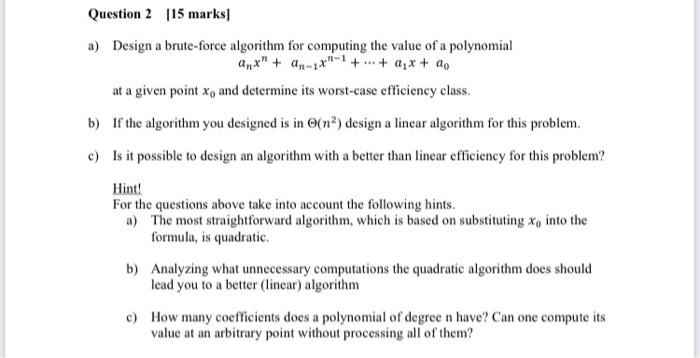
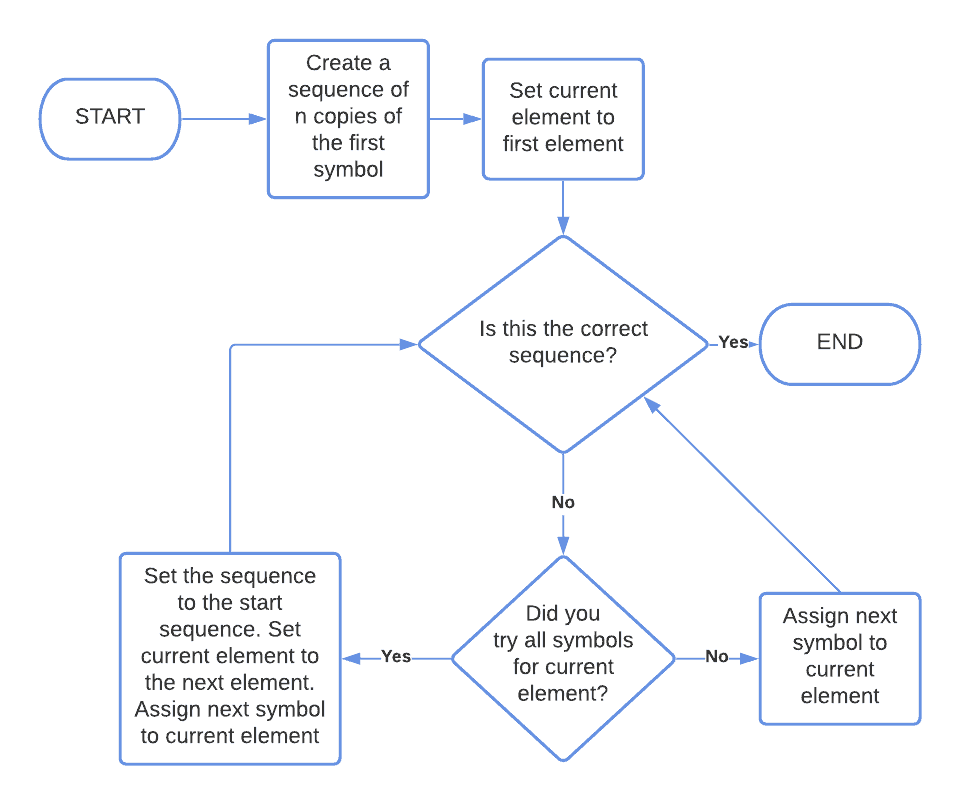
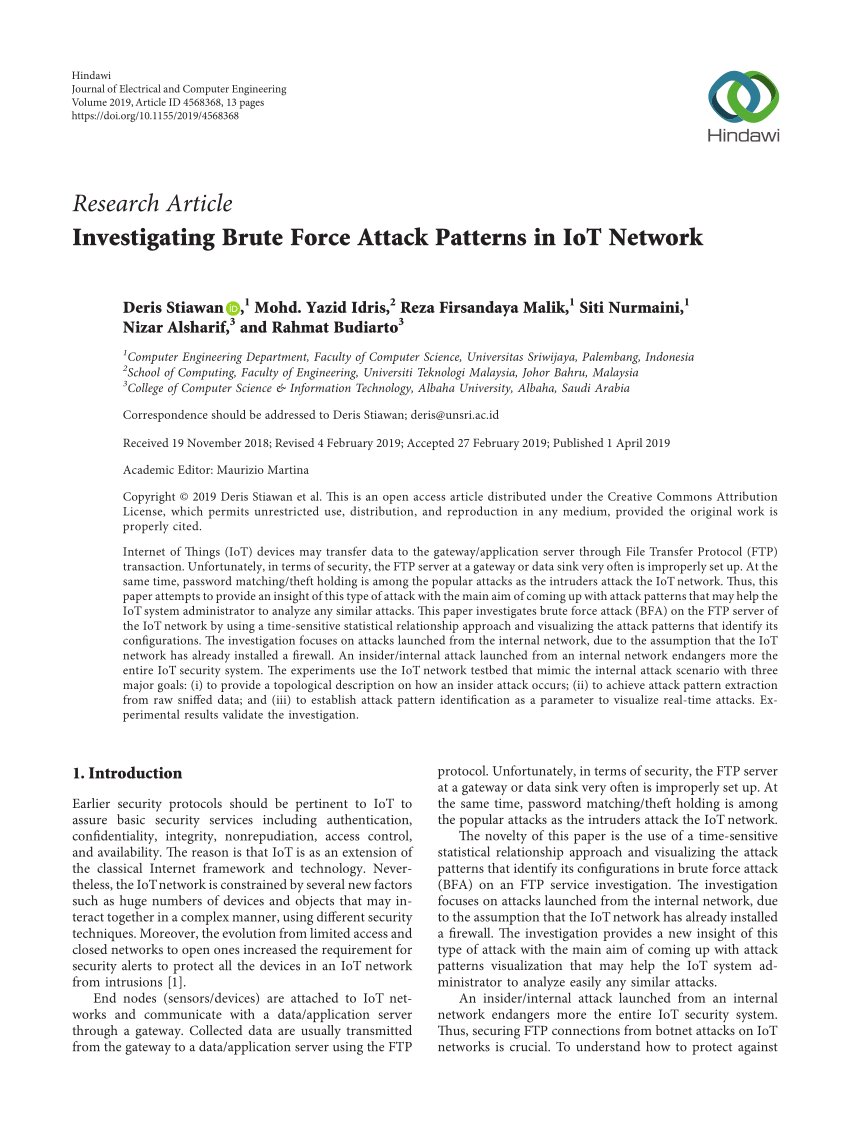
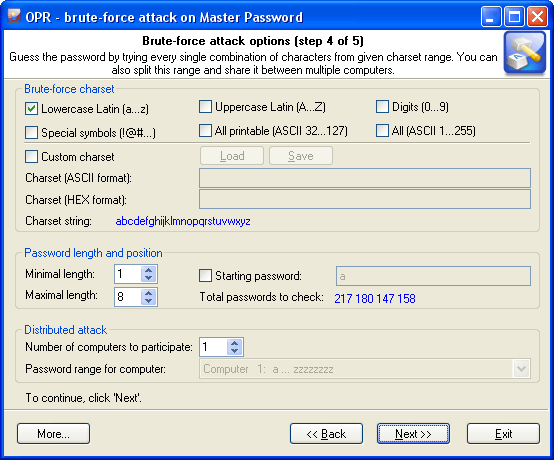
Design and Analysis of Algorithms - Chapter 31 Brute Force A straightforward approach usually based on problem statement and definitions Examples: 1. Computing. - ppt download