Amazon.com: Adamant Custom 16-Core Liquid Cooled Gaming Desktop Computer PC Intel Core i9 12900K 3.2GHz Z690 Prime Series 32Gb DDR5 1TB NVMe PCIe 4.0 SSD 4TB HDD 850W WiFi Bluetooth Geforce RTX
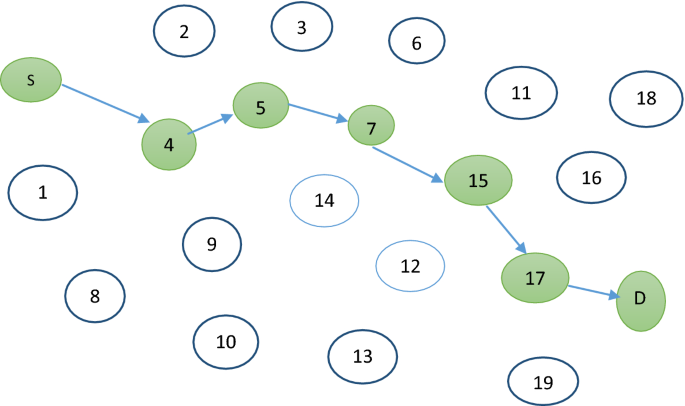
Resource key distribution and allocation based on sensor vehicle nodes for energy harvesting in vehicular ad hoc networks for transport application | SpringerLink

Haker I Cyfrowy Kod Binarny W Tle Koncepcja Cyberprzestępczości Ilustracji - Ilustracja złożonej z programu, hasło: 179884927
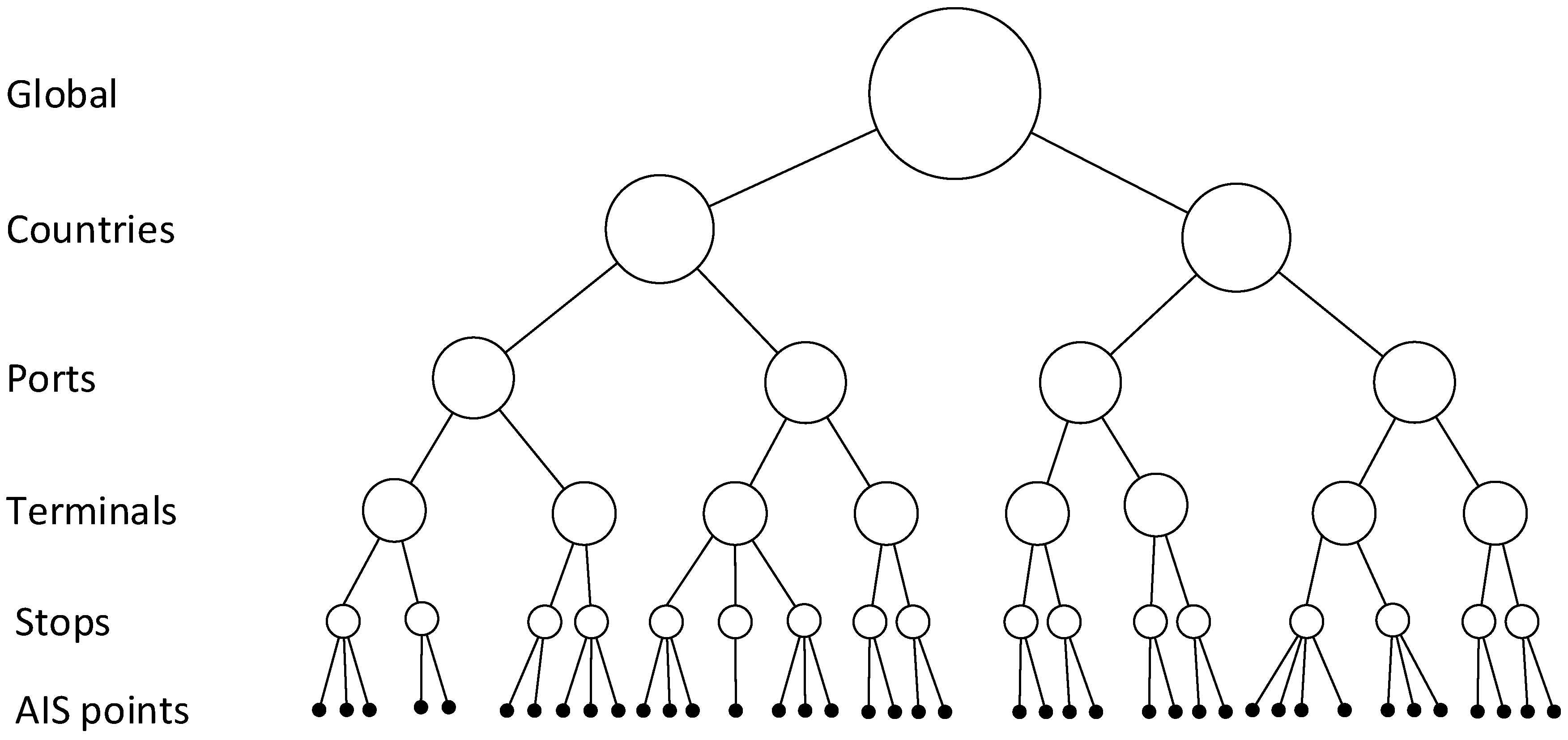
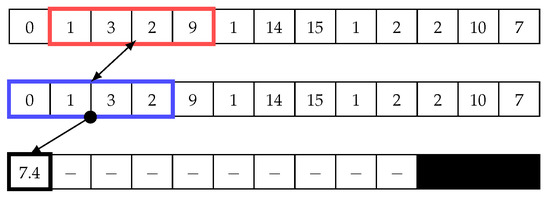
Sensors | Free Full-Text | Extracting Global Shipping Networks from Massive Historical Automatic Identification System Sensor Data: A Bottom-Up Approach | HTML
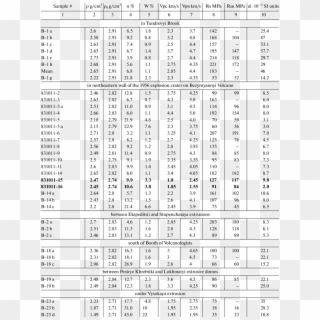
The Physicomechanical Properties Of Rocks In The Bezymyannyi - Kod Binarny, HD Png Download - 850x1118(#4652493) - PngFind
Algorithm Symbols Stock Illustrations – 1,605 Algorithm Symbols Stock Illustrations, Vectors & Clipart - Dreamstime

Bag of textual graphs (BoTG): A general graph‐based text representation model - Dourado - 2019 - Journal of the Association for Information Science and Technology - Wiley Online Library